Dr Marietta Ulrich-Horn, Managing Director and Head of the R&D Department at SECURIKETT® Ulrich und Horn GmbH, Münchendorf (Austria), sees tamper protection as the central challenge of product protection. Without a reference to first opening, any kind of authentication feature becomes pointless. The company has developed an all-in-one label that combines the most common technologies.
A label that can be removed without destroying it in order to reuse it on other packaging does not protect the contents of the packaging. If the detached label is reused on a counterfeit product, the counterfeit is mistaken for an original.
For the Tamper protection constant further development is essential in order to stay one step ahead of counterfeiters. For high-risk markets and products, Dr Marietta Ulrich-Horn recommends the proprietary VOID technology. This separates several layers of colour when a label is peeled off, causing a previously unrecognisable font or pattern to appear. The VOID effect can also be triggered by heat or liquid.
Additional features are used for authentication on the basis of sufficient security against manipulation. The risk assessment provides information about the required level of complexity of the Authentication features, from overt (holograms/DOVIDS) to covert (microtext, security inks) to forensic (taggants/chemical markers).
Codes are also increasingly being used as a digital security feature. Codes can be printed visibly on the label or covered so that they are only exposed after a covering layer has been removed. A very complicated design is offered by the SECURIKETT® developed Vienna-VOID. It combines two VOID effects (colour changes) for proof of opening at different levels. A security code can be covered on the upper level to prevent tampering. At the same time, another VOID effect is triggered if not only the code cover but the entire label is removed or tampered with. A pilot project is currently underway in which the Vienna VOID is being used for high-end spirits on the Chinese market.
Authentication is increasingly supported digitally - through product identity codes
In this way, digital product protection makes it possible to identify and track each individual product at „item“ level. The prerequisites for this are the guaranteed uniqueness of the codes and appropriate data management. The CODIKETT internet platform® from SECURIKETT® provides the generation of unique codes, as well as verification via smartphone and an extensive application portfolio for the brand owner.
Through Track & Trace The actual distribution channels are disclosed throughout the entire supply chain. Current weak points, such as the infiltration of counterfeit products into the distribution channels or grey trade, are uncovered. The data analysis of all product movements also provides valuable market data for the sales, supply chain and marketing departments. Even low scan rates of one to five per cent of all products are sufficient to uncover product piracy. But who scans the codes to provide the necessary data?
In the first step, the codes are activated by the manufacturer before dispatch in order to assign the relevant information to them (product information, target market, distributor, etc.). Encouraging distributors to scan is relatively easy for brand manufacturers, as they can oblige them to do so via the dealer contracts. Distributors with a „clean slate“ are also interested in disclosing their correct distribution channels. In addition, a brand manufacturer can send out „inspectors“ to scan products on the market and collect targeted data.
The end customer must Added value be communicated in particular. Brand manufacturers should communicate their product protection measures accordingly and point out that the code contains valuable information for the customer. If the code is scanned with a mobile phone, a response page appears, which primarily provides information on the originality of the product. Additional product-specific content, images or videos can be integrated. Scanning the codes should be perceived as positive by the customer and create a feeling of security and added value.

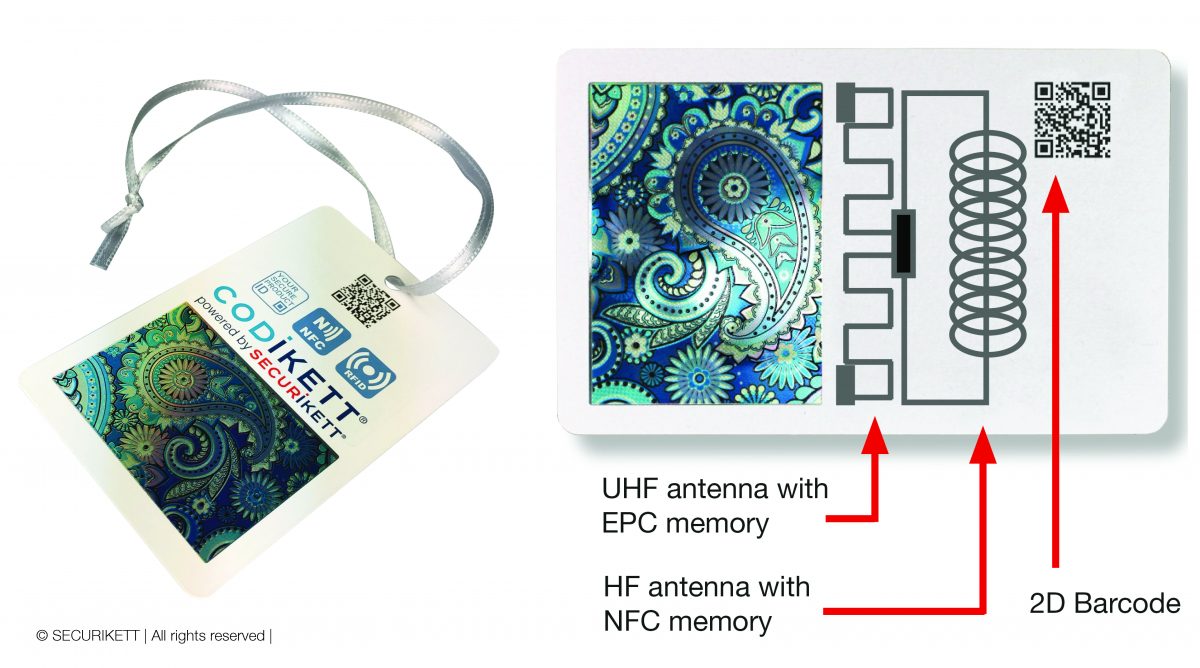
„Interoperability is a core concept in the age of Industry 4.0. We need to be open to the interaction of different systems and media,“ says Dr Marietta Ulrich-Horn, explaining the strategic background to the latest product innovation.
Plug & play with information carriers such as QR code, RFID or NFC
It is important to make access to the code information as easy as possible. New technologies such as NFC or RFID contribute to user-friendliness when scanning.
Not only do different user groups require different information, they often use different devices to scan codes. The interesting thing about UHF RFID is the access to the EPC memory and the possibility of bulk reading at a radio frequency of 850 to 950 MHz. Above all, it facilitates handling in logistics, packaging aggregation and rolling inventory. In order to User friendliness In order to facilitate communication with consumers or product authentication, the printed QR code or the NFC chip (13.56 MHz) is more commonly used. This is already enabled for many smartphones.
[infotext icon]Risk assessment of counterfeit productsRisk management is an essential part of every company. The ISO22380 standard on „general principles for product fraud risk and countermeasures“ provides a good tool for assessing risks with regard to manipulation, counterfeiting, piracy and grey markets in the various markets. This will be published in 2018 and can then be purchased from ISO.

The graphic contained in the standard shows that the brand manufacturer can only intervene in the area of „guardianship“. Effective protective measures to prevent counterfeit products are required[/infotext].
All images: © SECURIKETT | All rights reserved